
A Healthy IT Infrastructure: The Foundation of Robust Cybersecurity
In an era where cybersecurity threats loom large and data breaches can have catastrophic consequences, it’s tempting to prioritize robust cybersecurity solutions above all else.
Improve your competitive advantage with our cloud deployment and optimization expertise
Reduce your risk and exposure to complex cyber threats by adopting our tailor-made cybersecurity solutions
Whether it’s a security threat, cloud data backup issue, lost email, our team is here to assist
Leave your IT service management to the global Managed IT provider so you can focus on your business development
Modernize your network infrastructure to work at the speed of your business
Software licensing, products and solutions from over 3000+ vendors and in multiple licensing forms

In an era where cybersecurity threats loom large and data breaches can have catastrophic consequences, it’s tempting to prioritize robust cybersecurity solutions above all else.

Sandboxing technology has emerged as a critical tool in the battle against malicious software and cyber threats in the ever-changing landscape of cybersecurity. This blog
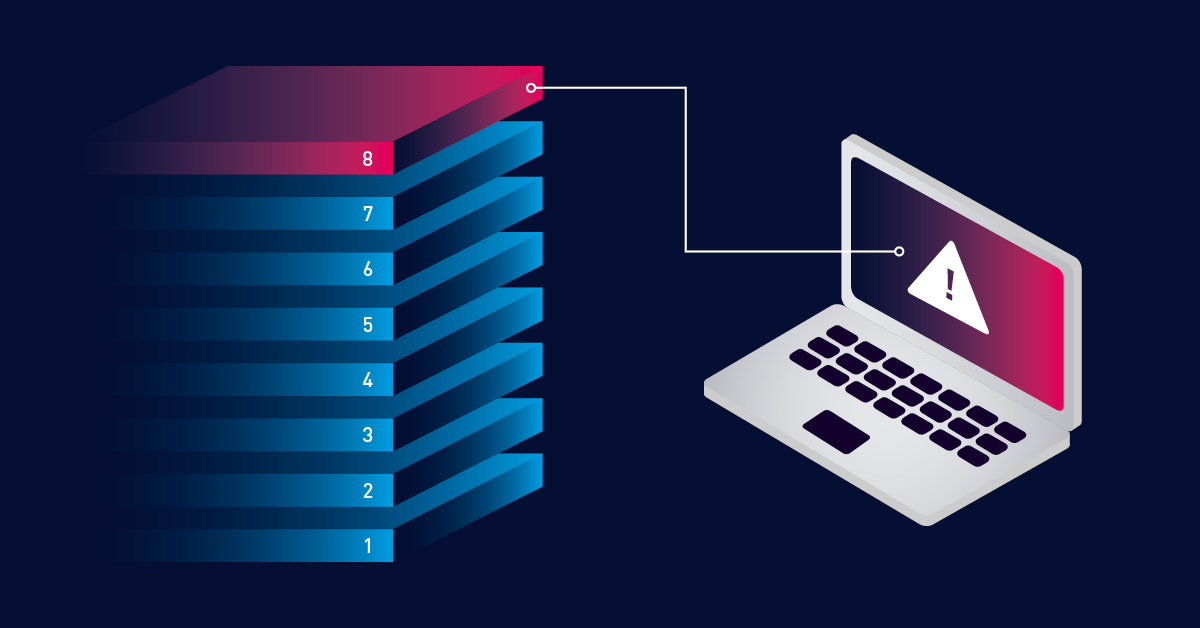
In the intricate realm of cybersecurity, understanding the OSI (Open Systems Interconnection) layer model is crucial for safeguarding digital systems and networks. The OSI model
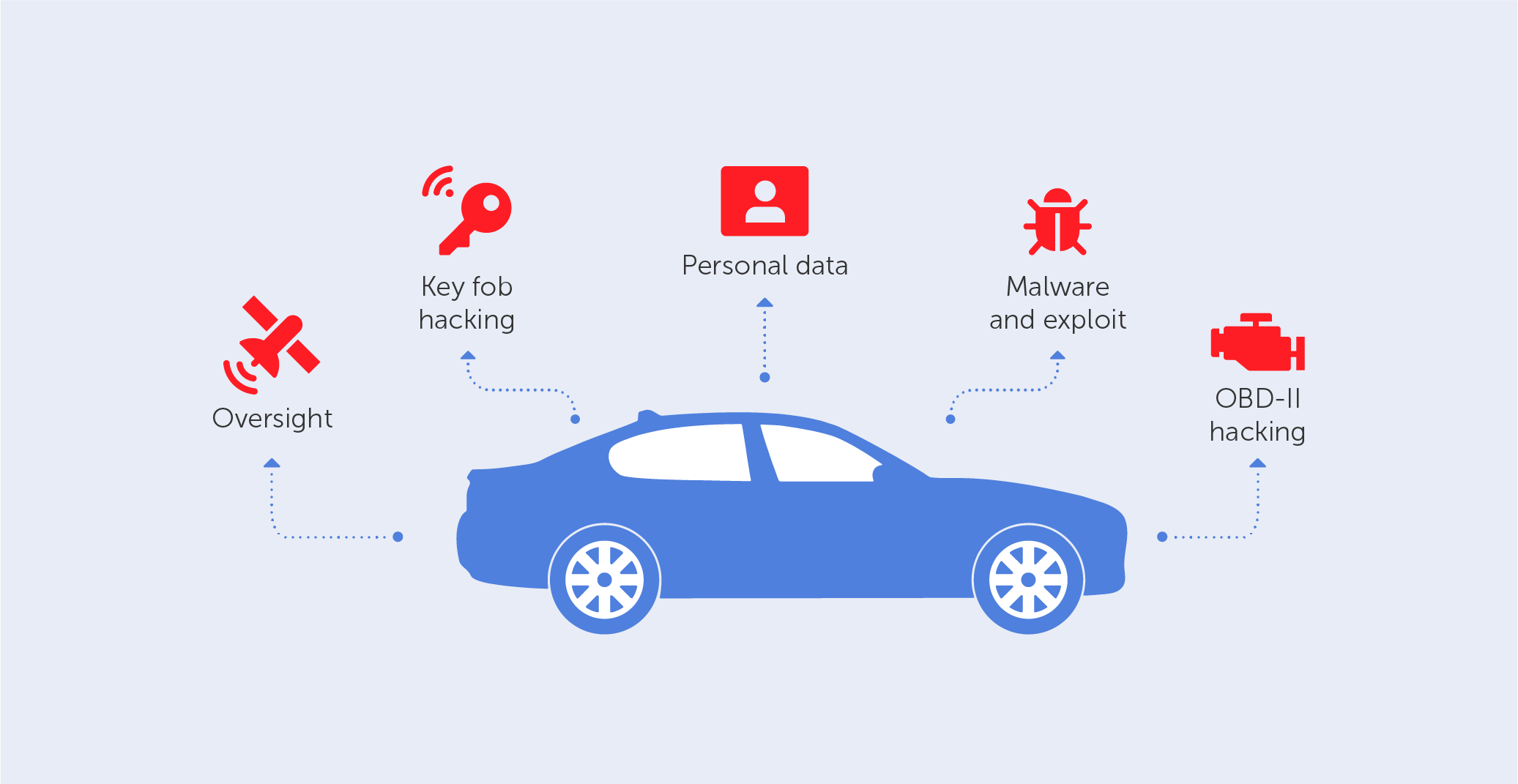
Imagine cruising down the highway, your favorite song playing through the speakers, while your car autonomously glides along in perfect harmony. But what if I

What is a botnet attack and how does it work? A botnet attack is a type of cyberattack that occurs when a group of internet-connected